Banks across Pakistan have been warned of a new global malware threat, Ploutus, capable of emptying Automated Teller Machines (ATMs) without accessing customer accounts. The advisory, issued by 1LINK, highlights that the malware gives attackers direct control over ATMs, enabling unauthorized cash withdrawals.
Ploutus attackers gain physical access using generic keys, then either copy malicious software onto the ATM’s storage device or replace it entirely. Once installed, the malware bypasses standard safeguards and can be adapted to work across different ATM models with minimal modifications.
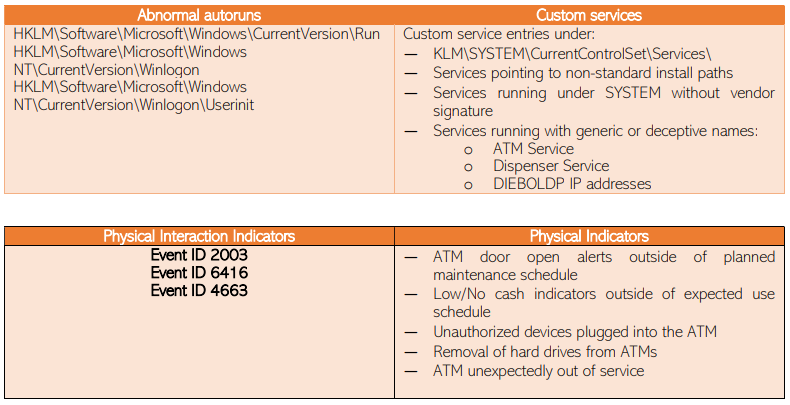
Indicators of compromise include suspicious .exe files, unauthorized remote access applications, abnormal autoruns, custom services, and unusual physical interactions, such as ATM doors opening outside scheduled maintenance or hard drives being removed.
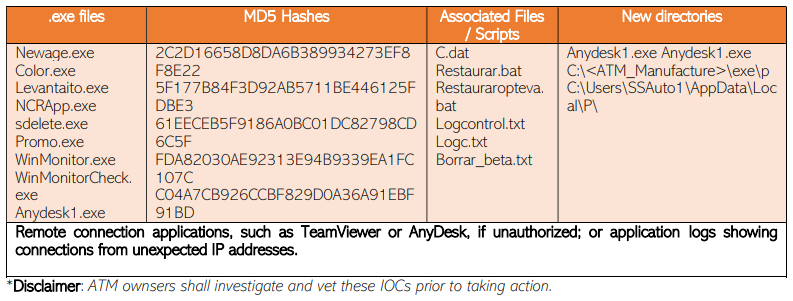
Other indicators:
Recommended security measures include:
- Physical Security: Upgrading locks, adding sensors, cameras, and barriers, and monitoring all unusual access.
- Hardware Security: Implementing disk encryption, firmware checks, memory protection, device whitelisting, and automatic shutdown on threat detection.
- Logical Access: Disabling external storage ports by default and allowing only approved access with continuous monitoring.
- Network Security: Whitelisting IPs, restricting software execution, and using endpoint detection tools.
- Logging & Auditing: Enabling advanced audit policies, maintaining centralized logs, and regularly auditing ATM systems.
- Prevention Practices: Changing default credentials, maintaining “gold images” of ATMs, and testing security measures in preproduction environments.
Authorities warned that without immediate action, Ploutus could enable large-scale ATM “jackpotting,” posing serious financial risks for banks and customers nationwide.